Executive Summary
Expert compilation on Kerberos (protocol). Knowledge base synthesized by Americanbible Data Intelligence from 10 verified references with 8 visuals. This analysis also correlates with findings on How Does Kerberos Work? The Authentication Protocol Explained to provide a broader context. Unified with 8 parallel concepts to provide full context.
Everything About Kerberos (protocol)
Authoritative overview of Kerberos (protocol) compiled from 2026 academic and industry sources.
Kerberos (protocol) Expert Insights
Strategic analysis of Kerberos (protocol) drawing from comprehensive 2026 intelligence feeds.
Comprehensive Kerberos (protocol) Resource
Professional research on Kerberos (protocol) aggregated from multiple verified 2026 databases.
Kerberos (protocol) In-Depth Review
Scholarly investigation into Kerberos (protocol) based on extensive 2026 data mining operations.
Visual Analysis
Data Feed: 8 Units
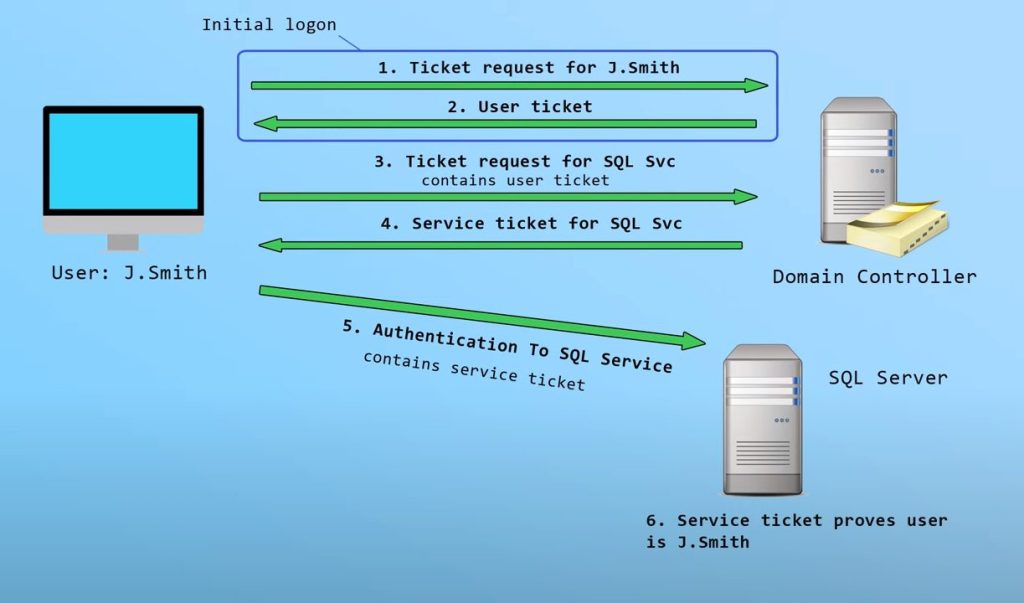
IMG_PRTCL_500 :: KERBEROS (PROTOCOL)
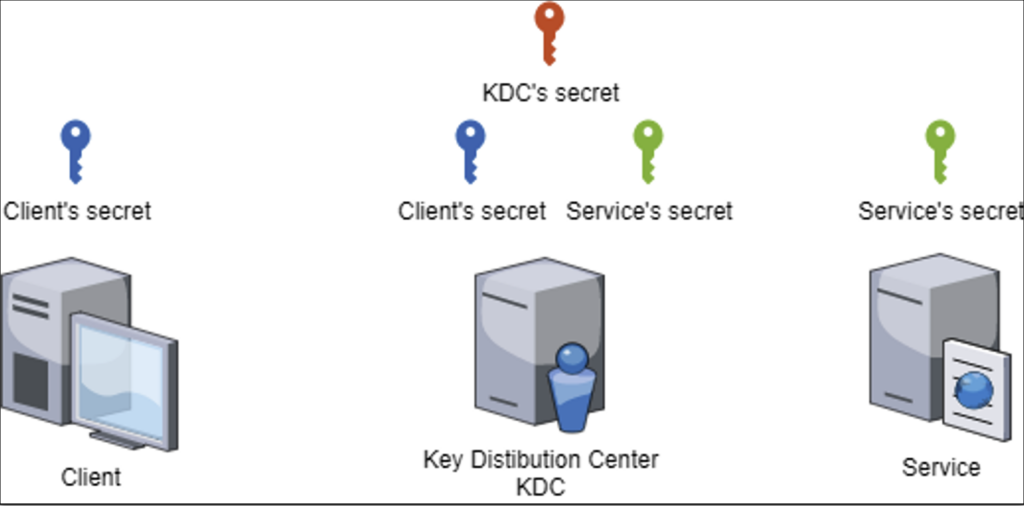
IMG_PRTCL_501 :: KERBEROS (PROTOCOL)

IMG_PRTCL_502 :: KERBEROS (PROTOCOL)

IMG_PRTCL_503 :: KERBEROS (PROTOCOL)

IMG_PRTCL_504 :: KERBEROS (PROTOCOL)

IMG_PRTCL_505 :: KERBEROS (PROTOCOL)
IMG_PRTCL_506 :: KERBEROS (PROTOCOL)
IMG_PRTCL_507 :: KERBEROS (PROTOCOL)
Key Findings & Research Synthesis
Analyze detailed facts about kerberos authentication overview. This central repository has aggregated 10 online sources and 8 media resources. It is integrated with 8 associated frameworks for maximal utility.
Helpful Intelligence?
Our neural framework utilizes your validation to refine future datasets for Kerberos (protocol).